Connecting devices to your Wi-Fi network is a simple task—but likewise, hackers do not have difficulty connecting to your network and prying into your traffic. You can minimize potential security risks by making the most of safeguards available in every Wi-Fi router.
Using Wi-Fi, we all send sensitive data—passwords, financial information, personal details, and even corporate credentials and information—onto the Internet, where the information can be stolen or used for identity theft. When your Wi-Fi network has a bandwidth cap, leaving your network open for everyone could result in additional charges, due to the extra usage from unknown persons. And an open network even gives people the ability to engage in illegal activity from your network, which can possibly put you at legal risk.
We recommend securing your Wi-Fi network with the following steps. Your specific router will determine exactly how to accomplish the tasks, but all should be easy to complete.
- Change Your Wi-Fi Router’s Default Password
All Wi-Fi routers have administrative interfaces for adjusting settings, including security options. The default passwords for these interfaces are well-known to hackers, so when setting up a new Wi-Fi router—or when assessing your current Wi-Fi router—you should change the password for accessing this admin interface.
- Change the Default Network Name (SSID)
Every Wi-Fi network has a name: a Service Set Identifier (SSID). Default names frequently identify the router’s manufacturer (such as ‘Netgear’ or ‘Linksys’), thus telling hackers which known vulnerabilities or password styles to use in their break-in attempts for particular routers. Change your network name to add a layer of security—and make your network easier to locate in lists of nearby networks.
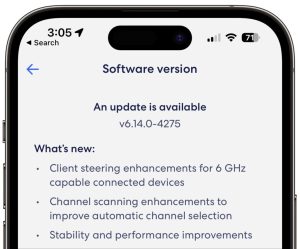
- Update Your Wi-Fi Router’s Firmware
Manufacturers of Wi-Fi routers regularly release new firmware versions and fix security weaknesses. Ensure your router has the latest firmware, and turn on the option to have its firmware updated automatically, if available.
- Disable Wi-Fi Protected Setup (WPS)
A technology called Wi-Fi Protected Setup (WPS) enables connecting to Wi-Fi networks without the password; rather, users can enter an 8-digit PIN or press a button on the router. While the latter option is just fine, the PINs are insecure and can be deciphered with easily obtainable cracking software. If your router supports WPS, turn this feature off entirely.
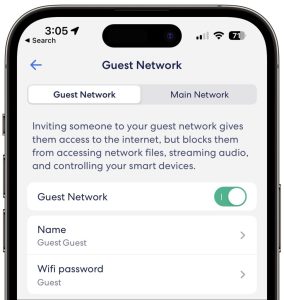
- Create a Guest Network
Give visitors access to your Wi-Fi network by creating a guest network, separate from your main Wi-Fi network. With a different name and password, a guest network isolates its traffic from yours, which makes certain that your communications will not be privy to hackers if they infiltrate it. Additionally, you should put devices like smart appliances, video game consoles, and the like on your guest network so they also cannot provide access to your main network’s traffic if hacked.
- Use Strong WPA2 or WPA3 Encryption
All traffic on a Wi-Fi network should be encrypted so that hackers do not have immunity to spy. The first wireless security protocol, called Wired Equivalent Privacy, or WEP, was used through 2004, but today it is no longer considered secure. Switch from WEP to Wi-Fi Protected Access, which is WPA2 or WPA3 encryption.
If you follow the advice in this article, there is no need to hide your SSID, which is also sometimes suggested as a security measure. Anybody who possesses the needed skills and software for breaking into unprotected, or weakly protected, Wi-Fi networks can still find and access hidden networks—and may even have his or her interest piqued by the fact that the network owner took the extra step to hide the network.
Finally, when you are on public Wi-Fi networks, use a Virtual Private Network (VPN) for complete certainty that all traffic is protected. VPNs create encrypted channels from your computer to VPN servers elsewhere. Many companies provide or require VPN use so traveling or remote employees cannot unknowingly use unencrypted connections. If your organization would like to set up a VPN, contact us for assistance.
(Featured image by iStock.com/CASEZY)
